
CYBER SECURITY

MACHINE TOOLS

SMART SOLUTIONS

BUSINESS CONSULTING
Accidental & Malicious Data Leak
Traditional DLP was built to stop accidental leaks.
Modern attacks are different — malicious insiders, compromised accounts, and advanced exfiltration can bypass manual rules, tagging, and legacy policy models.
That’s why Augmenter brings GC Cybersecurity’s 4th Generation DLEP (GhangorCloud ISE) — a platform that automatically identifies sensitive data, classifies it in real time, and enforces policy inline as data moves across users, devices, repositories, and cloud apps.

Why 4th Generation DLEP?

Limited Protection Scope
Legacy DLP mostly focuses on accidental leaks — it struggles against intentional exfiltration and sophisticated breach scenarios.
High Failure Rates
Manual rule tuning and user-dependent actions lead to false positives, missed leaks, and policy failures.
Process Inefficiency
Traditional approaches depend on manual tagging/classification, increasing operational load and human error.
Trivial CASB Capabilities
Basic CASB-style controls often provide surface-level coverage, without deep automation and real threat prevention.
Augmenter’s Solutions
Automated Data Identification
Automatically discovers and identifies sensitive information across the enterprise — no manual tagging required.
Advanced Threat Analysis
Detects anomalous and malicious data leak behaviors from both insiders and outsiders.

Intelligent Data Classification
Real-time classification using content and context — including “new/virgin” data — to improve detection accuracy from day one.
Automated Policy Enforcement
Policies are synthesized/enforced automatically and applied inline as data moves — reducing reliance on complex manual policy building.
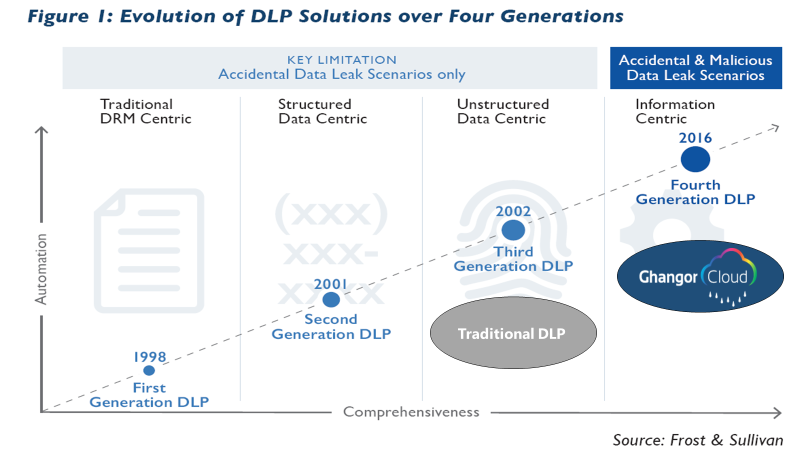
Evolution of DLP Solutions
From “reactive DLP” to real-time DLEP
GC Cybersecurity’s platform represents the shift from legacy DLP (manual, rule-heavy) to 4th Generation DLEP — where protection is driven by:
- Inline processing (controls where data moves)
- End-to-end automation (less manual tuning)
- Protection against accidental + malicious scenarios
- Centralized management and visibility
This is why 4th Gen DLEP is designed to close the gaps that legacy DLP leaves open — especially against malicious exfiltration.
Key Benefits
Advanced Access Control
Auto classification of Data
Policy Enforcer
Governance & Regulatory Compliance
Experience 4th Generation DLEP with Augmenter Consulting — built for modern enterprises where data moves fast and threats move faster.
Copyright © 2025 Augmenter Consulting. All Right Reserved






